Get encrypted instance¶
The service provides the possibility to encrypt the storage volume associated to the virtual machine on-demand.
Warning
Only the external volume, where Galaxy data are stored, is encrypted, not the Virtual Machine root disk.
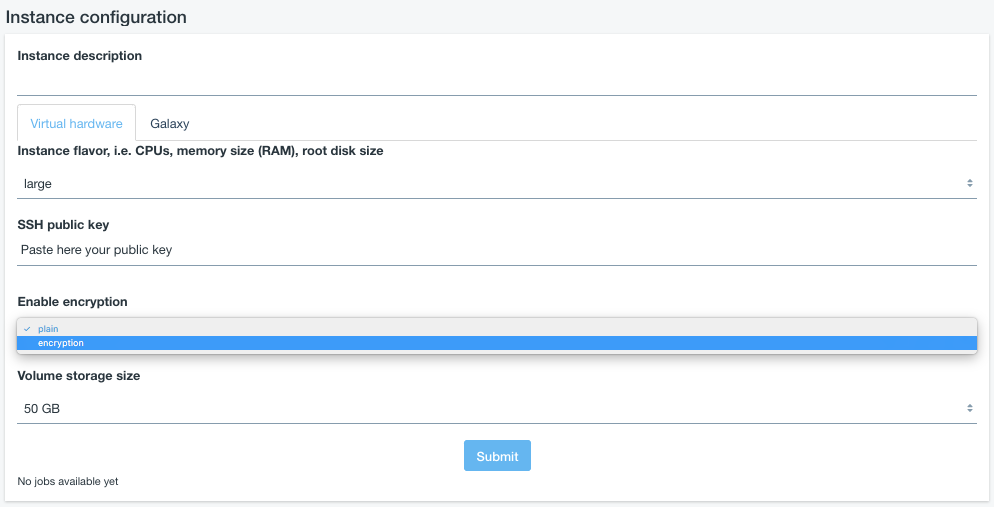
To encypt the external volume storage flag encryption in Enable encryption box.
Cryptographic keys should never be transmitted in the clear. For this reason during Galaxy deployment user intervention is required.
Data privacy is granted through LUKS storage encryption: user will be required to insert a password to encrypt/decrypt data directly on the virtual instance during its deployment, avoiding any interaction with the cloud administrator(s).
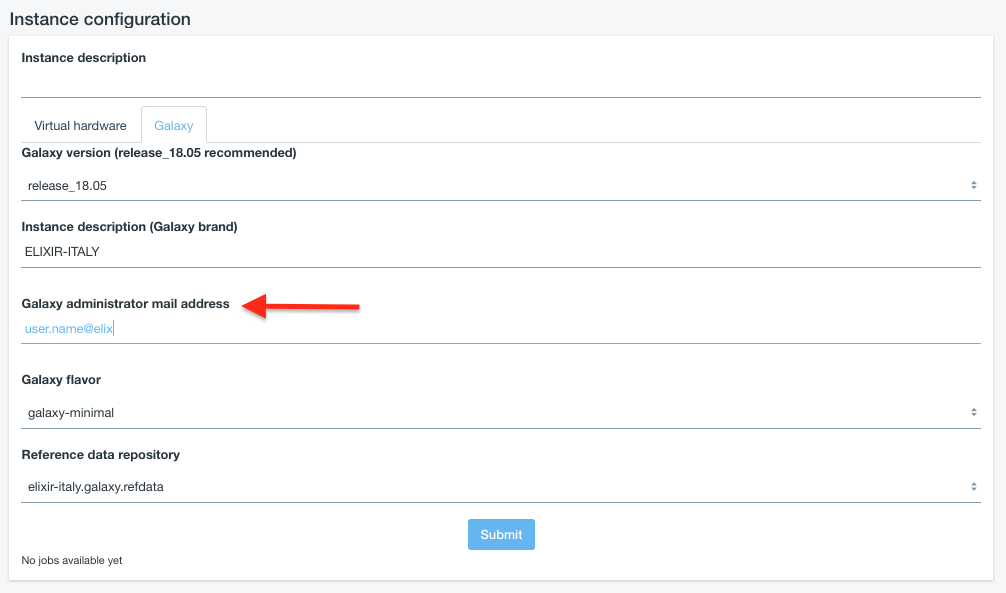
An e-mail is sent to instance administrator the e-mail address configured in the Galaxy Configuration section.
Warning
Make sure you have entered a valid mail address!
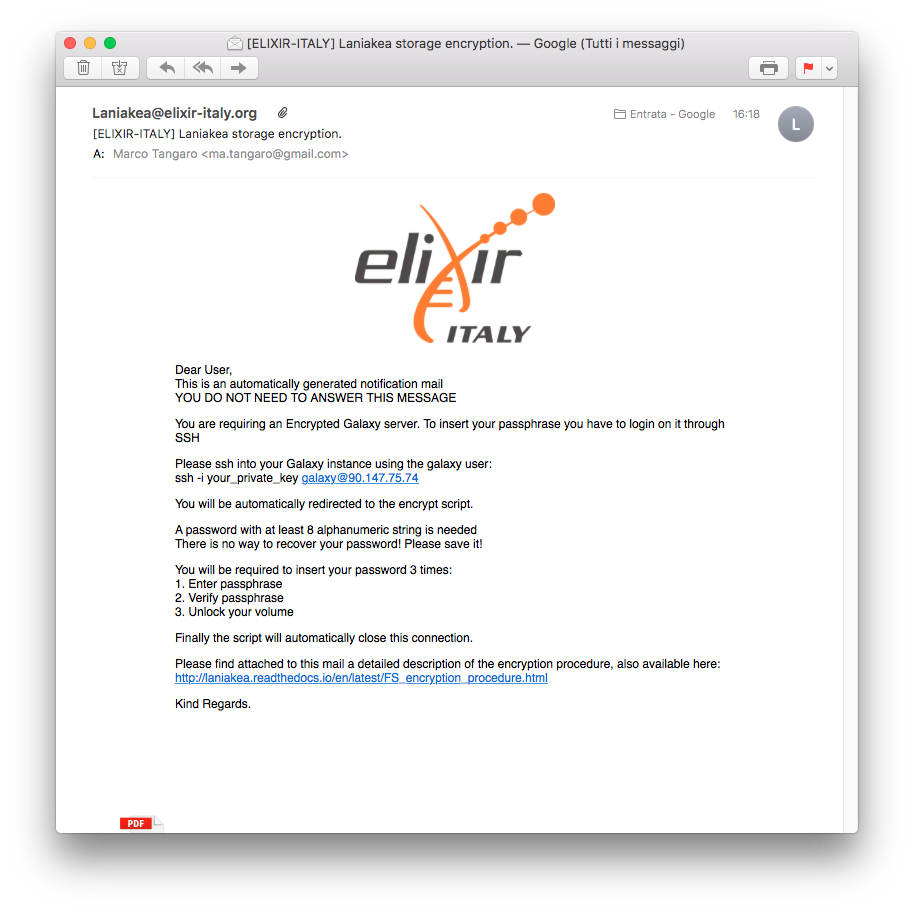
The e-mail is sent you only when the system is ready to accept your password and contains all the instructions to correctly encrypt/decrypt your system. The e-mail subject is [ELIXIR-ITALY] Laniakea storage encryption, sent by Laniakea@elixir-italy.org
Warning
If you don’t receive the e-mail:
- Check you SPAM mail directory
- Chek mail address spelling
- Wait 15 minutes more.
Once the e-mail is arrived you can follow the step by step guide to encrypt your volume: Storage encryption procedure.
User is only asked to insert their alphanumeric password 3 times:
- Set password
- Confirm password
- Open LUKS volume.
After the password injection the logout is automatic: the encryption procedure continues in background.
Default encryption algorithm¶
The default LUKS configuration are:
Cipher: aes-xts-plain64
Key size: 256 bit
Hash Algorithm for key derivation: sha256
See also
For a detailed description of all Web UI options see section: Laniakea options.